The best emergency is the one that never happens. For everything else, a strong risk mitigation plan is what helps your people, operations, and business recover faster. Below are 10 practical risk mitigation strategies, real-world examples, and a free planning template.

10 Risk Mitigation Strategies & Examples for 2026

When Hurricane Harvey approached the Gulf Coast in 2017, the team at Gulf Coast Regional Blood Center did not have the option to pause operations. Hospitals across the region urgently needed blood to treat a growing number of injuries. Using their emergency communication system, the organization coordinated ad hoc procedures, communicated with drivers and donors in real time, and adapted operations during one of the worst storms in U.S. history.
That is the essence of risk mitigation. The storm itself could not be prevented. Through preparation, communication infrastructure, and disciplined decision-making, the organization reduced disruption and continued operating under extreme conditions.
Every organization faces unavoidable risks. Severe weather, cybersecurity incidents, workplace violence, supply chain disruptions, civil unrest, and other operational risks all threaten business continuity and employee safety. A 2025 AICPA and NC State University report found that 61% of senior finance leaders say the volume and complexity of risks have changed “mostly” or “extensively” over the past five years.
The goal of risk mitigation is not to eliminate every risk. That is impossible. Resilient organizations focus instead on reducing the likelihood, severity, and operational impact of threats before they escalate into full-scale crises.
Download Our Risk Mitigation Plan Template
What Is Risk Mitigation?
Risk mitigation is the process of identifying, assessing, and reducing threats that could negatively affect an organization. A robust risk mitigation plan helps organizations limit operational disruption, protect employees, contain financial losses, and recover more quickly when incidents occur.
Effective risk mitigation strategies focus on two objectives at once:

- Reducing the likelihood that a threat or disruption occurs
- Limiting the operational, financial, reputational, or safety impact when one does occur
What this looks like depends on the threat. To mitigate the risk of workplace violence, organizations may conduct workplace violence training, harden facilities to reduce vulnerabilities, and rehearse response protocols with employees. To mitigate severe weather risks, organizations may monitor storms in real time, rehearse evacuation plans, secure facilities ahead of impact, and maintain two-way communication with employees throughout the incident.
The risks each organization faces vary by industry, geography, and operating model. The job is to identify those risks honestly, understand the corresponding vulnerabilities, and address them proactively.
Common Risk Mitigation Examples
Risk mitigation in practice covers a wide range of activities. Common examples organizations rely on include:
- Conducting employee safety and security training
- Running tabletop exercises and live drills
- Implementing cybersecurity monitoring and access controls
- Segmenting networks and isolating high-risk systems
- Maintaining backup suppliers and redundant inventory
- Purchasing insurance to transfer financial exposure
- Monitoring severe weather and geopolitical conditions
- Developing business continuity and contingency plans
- Establishing two-way emergency communication channels
Most resilience programs combine several of these activities, layered across the same threat. The 10 strategies below show how organizations select and apply them.
Risk Mitigation vs. Risk Prevention
Risk prevention and risk mitigation are closely related but not the same thing.
- Risk prevention focuses on preventing incidents from occurring in the first place.
- Risk mitigation focuses on reducing the likelihood or impact of incidents that cannot be fully prevented.
Mature resilience programs use both. Prevention measures reduce exposure to threats, while mitigation strategies enable organizations to keep operating and recover quickly when disruptions occur.
What Are the Four Types of Risk Response?
When a risk surfaces, organizations generally have four ways to respond. Most mature programs use all of them, applied to different threats based on likelihood, impact, and what can reasonably be controlled.
- Risk avoidance. Eliminate the threat by not engaging with the activity that creates it. Canceling a business trip in the path of a hurricane is one example.
- Risk transference. Shift some or all of the financial impact of a risk to a third party. Insurance is the most common example.
- Risk acceptance. When a risk is small enough, the most rational move can be to let it play out. The key is making that choice deliberately and knowing where tolerance ends.
- Risk mitigation. Many risks are neither avoidable nor acceptable, and not all of the impacts can be transferred. For these, organizations mitigate by reducing the chance of occurrence, the severity of impact, or both.
A workplace fire illustrates how all four work together. Avoidance looks like a no-open-flames policy in office space. Transference is property and liability insurance. Acceptance is the residual risk left after every reasonable control is in place. Mitigation includes smoke detectors, sprinklers, evacuation routes, fire drills, and the two-way communication that activates when an emergency does occur.
The Risk Mitigation Process
Most organizations follow a structured process to translate risk awareness into action:
- Identify risks and vulnerabilities.
- Assess likelihood and operational impact.
- Prioritize risks using a risk matrix.
- Select mitigation strategies and controls.
- Implement response procedures and safeguards.
- Continuously monitor evolving conditions.
- Test, refine, and improve plans over time.
Steps 1 through 3—identification, assessment, and prioritization—set the trajectory for everything that follows. Time, budget, and headcount are always finite, and that scarcity is itself a risk-management problem. Scott Davidson, CEO and Founder of Code 4, captured the dilemma well in an interview for The Employee Safety Podcast:
“Even the most thoughtfully planned, well-funded, and longstanding events have a scarcity of resources. Our job is to really triage and be futurists, tasked with predicting the future based on our expertise, experience, and the patterns and trends we’re observing. We have to identify what risks are worthy and meaningful to mitigate against and knowingly leave some unmitigated.”
The way through that triage is structured prioritization. A risk matrix that plots likelihood against impact gives organizations a defensible basis for sequencing.
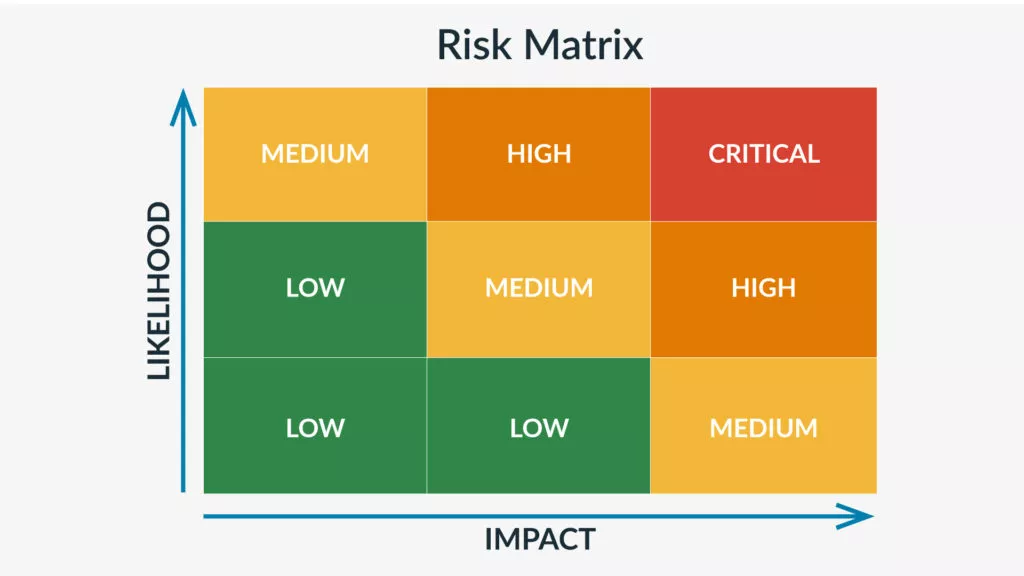
Consider an Alaskan king crab boat working in heavy seas. A crew member going overboard carries a high likelihood and a catastrophic impact. That is a critical risk and the top priority for mitigation. GPS equipment failure is unlikely with proper maintenance and has a moderate impact, since the crew can navigate by other means. That is a medium risk worth mitigating with backup tools. Eggs breaking in the kitchen are likely on rough seas, but the impact is low. That is a risk the team can absorb with a quick cleanup and move on.
Pairing the matrix with a business impact analysis gives leaders the information they need to choose where mitigation effort will pay off most.
8 Common Types of Business Risk
Every organization faces a slightly different mix, but most enterprise risk inventories return to these eight categories:
- Operational risk. Internal processes, systems, or external events that disrupt daily operations.
- Strategic risk. Poor decisions or a failure to adapt to industry change that affects long-term goals.
- Financial risk. Losses from market volatility, fraud, credit exposure, or liquidity challenges.
- Safety risk. Harm to the physical safety of employees, contractors, customers, or visitors.
- Security risk. Theft, breaches, vandalism, workplace violence, or unauthorized access to physical or informational assets.
- Human risk. Errors, turnover, misconduct, or capability gaps inside the organization.
- Compliance risk. Penalties or operational disruption from failure to comply with laws, standards, or contracts.
- Reputational risk. Erosion of customer trust, often as a downstream effect of one of the categories above.
Most real-world incidents touch more than one of these categories at the same time. A cyberattack is a security incident with operational, financial, and reputational tails. A workplace fire is a safety incident with operational, financial, and compliance consequences. Designing a plan around the categories, not just specific threats, is part of what makes it resilient.
10 Risk Mitigation Strategies and Examples
Effective risk mitigation plans rarely rely on a single tactic. Most organizations layer multiple strategies together to reduce operational disruption and strengthen resilience across the business.
1. Manage escalating risk
Strategy: Some threats evolve gradually and can be monitored in real time. Organizations can continue operating while conditions remain manageable, then scale back before the situation becomes unsafe.
Example: Retailers often remain open during the early stages of a snowstorm but close operations before road conditions become hazardous for employees and customers. The same pattern applies to climate-driven disruptions of all kinds, where staged decisions on opening, closing, and rerouting depend on conditions that change by the hour.
2. Prioritize risks
Strategy: When multiple risks emerge simultaneously, organizations must prioritize based on potential impact to people, operations, and critical assets.
Example: During a hurricane, a hospital first focuses on patient and employee safety, then on protecting facilities and equipment, and finally on administrative functions. Prioritization is what speeds up decision-making in the moment.
3. Test and rehearse response plans
Strategy: Tabletop exercises, drills, and simulations help organizations identify weaknesses before real incidents occur.
Example: Fire drills frequently uncover evacuation bottlenecks, accessibility challenges, or communication failures that would otherwise remain hidden until an actual emergency. Surfacing those gaps in a controlled rehearsal is far cheaper than learning them during a live event.
4. Isolate the risk
Strategy: Some risks cannot be eliminated, but they can be contained to reduce the scope of potential damage.
Example: Cybersecurity teams isolate public-facing systems from internal infrastructure using network segmentation and layered access controls. A compromise of the public surface no longer gives an attacker access to the rest of the environment.
5. Eliminate the risk
Strategy: When a threat presents unacceptable consequences, organizations may decide to remove the source entirely. This is risk avoidance applied at the process level.
Example: A manufacturer using a highly toxic solvent may switch to a safer alternative chemistry altogether, eliminating the underlying hazard rather than building increasingly expensive controls around it.
6. Buffer the risk
Strategy: Adding redundancy—time, staffing, financial reserves, or backup resources—can reduce operational fragility and improve resilience.
Example: Construction teams may add spotters, extend timelines, and provide backup equipment when lifting heavy machinery into high-risk areas. The work still carries inherent risk, but the buffer makes that risk manageable.
7. Quantify the risk
Strategy: Many business opportunities come with potentially costly risks. Organizations need to weigh risks against potential rewards and operational realities and revisit the math as conditions change.
Example: A delivery business may continue operations during light rain because the revenue opportunity outweighs manageable safety risks. The same business will suspend deliveries during a severe winter storm, where the reward is small and the chance of a bad outcome is high. Most decisions live between those two cases, which is why having a framework matters more than getting any single call perfect.
8. Monitor the risk
Strategy: Threats evolve continuously. Real-time monitoring helps organizations respond faster and make better-informed decisions, especially as the threat landscape shifts to include AI-enabled phishing, deepfake impersonation, and coordinated misinformation campaigns alongside more traditional risks.
Example: During civil unrest, organizations can combine real-time threat intelligence with two-way employee communication to coordinate shelter-in-place or evacuation decisions. The same combination supports faster response when emerging digital threats target employees or executives.
9. Develop contingency plans
Strategy: Primary plans do not always hold under rapidly changing conditions. Organizations need documented backup procedures, with clear activation criteria, for the scenarios their primary plans cannot cover.
Example: Travel risk management programs often include alternate transportation, lodging, and evacuation procedures for use when geopolitical conditions, supply chain disruptions, or environmental conditions deteriorate unexpectedly. Pre-arranged alternatives turn a sudden change of plans into an inconvenience rather than a crisis.
10. Leverage industry best practices
Strategy: Most of the risks an organization faces are not new. Established frameworks from OSHA, FEMA, ISO, and the National Safety Council provide proven guidance.
Example: Construction firms frequently rely on OSHA standards, inspection checklists, and training programs to reduce safety incidents and strengthen compliance. Adopting and integrating those standards into onboarding, supervision, and audits delivers much of the benefit without expensive trial and error.
Putting Your Risk Mitigation Plan Into Action
Risk mitigation is not a one-time exercise. Effective programs evolve continuously alongside changing operational conditions and emerging threats. Organizations that maintain strong resilience programs typically:
- Review and update plans on a fixed cadence—quarterly for high-velocity risks like cyber, civil unrest, and weather, and annually for the broader plan.
- Tie mitigation strategies to real-time monitoring so leaders know when to activate the plan.
- Conduct regular emergency drills and tabletop exercises to surface gaps before incidents happen.
- Maintain fast, two-way communication channels that are ready to use when something does go wrong.
- Run after-action reviews following incidents and exercises, and feed the findings back into the plan.
Many organizations already understand their largest risks. The real challenge is translating awareness into operational readiness before an incident occurs. With the right planning, communication systems, and operational discipline, organizations can reduce disruption, protect employees, and recover faster when emergencies happen.






