Your building’s layout, workflows, and location inform its risks. A physical security assessment can translate those unique factors into targeted security upgrades.

How to Conduct a Physical Security Assessment in 9 Steps
Physical security is often reduced to checklists: locked doors, functioning alarms, and cameras at entrances. While these fundamentals matter, true protection requires deeper insight—understanding how your facility’s unique layout, operations, and organizational changes create invisible vulnerabilities.
“Security is very reactive. With a flexible plan, you can change direction on a dime. Ensure you have the right technology and staff trained to take advantage of it—and always look out for better tools.”Joe Holokan Manager of Central Region Security, Cox Enterprises
That flickering light in the stairwell? The loading dock door that won’t latch? Outdated evacuation maps after a restructuring? These aren’t just minor oversights but contextual gaps that expose your people, assets, and reputation to risk.
As security professionals, our role isn’t just to react to threats but also to proactively anticipate how our environments enable them.
This article explains how a context-driven physical security assessment identifies these hidden exposures and provides a template for turning insights into tailored safeguards.
9-Step Physical Security Assessment
- Define your assessment’s scope
Establish the boundaries and objectives of the assessment to ensure a comprehensive and focused approach. - Inspect your facilities and sites
Evaluate the physical spaces to identify strengths and weaknesses in protective measures. - Audit your physical security systems
Assess the effectiveness of existing security systems and identify areas for improvement. - Review your operating procedures
Ensure that your organization’s procedures align with its security goals. - Identify physical security risks
Analyze internal and external factors to identify potential threats and vulnerabilities. - Anticipate insider threats
Assess vulnerabilities that insiders could exploit and implement preventive measures. - Assess specific threats and vulnerabilities
Evaluate the likelihood and impact of identified threats to prioritize mitigation efforts. - Document and report on your assessment
Create detailed reports of findings and recommendations to facilitate communication and future assessments. - Review and update regularly
Conduct regular reviews to adapt to evolving threats and ensure the effectiveness of security measures.
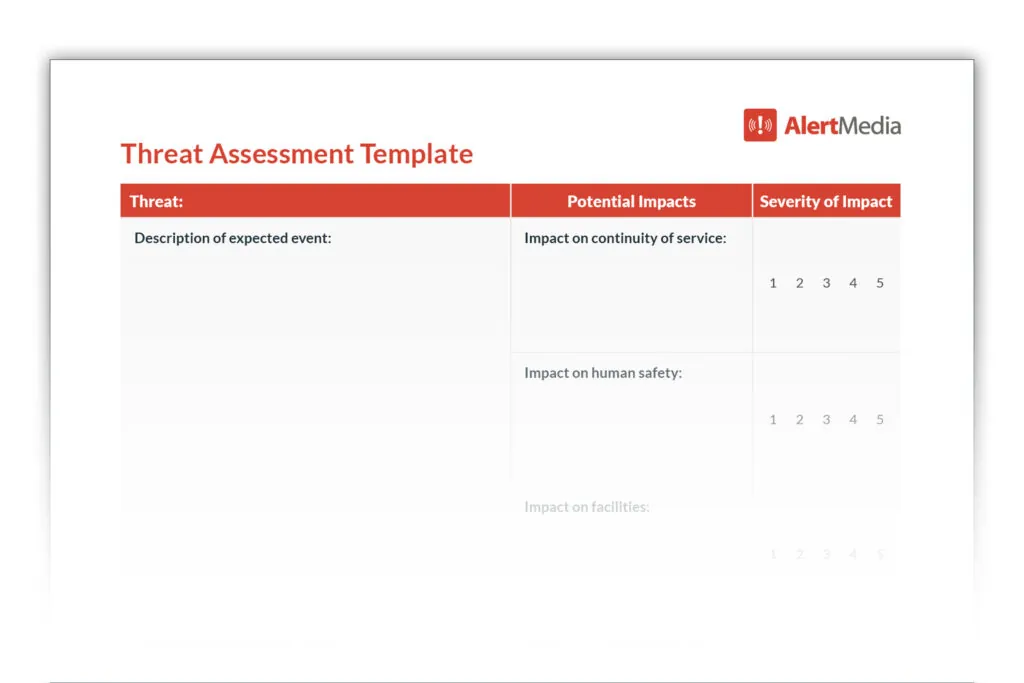
Download Our Threat Assessment Template
What Is a Physical Security Assessment?
A physical security assessment is a comprehensive audit of your organization’s physical security measures protecting your facilities, personnel, and assets. The assessment process evaluates your security systems and procedures relative to the threats and risks you face and recommends ways to improve physical security in the workplace. While security should be an organization-wide focus and cyber threats are more important to address than ever, network and IT security are outside the scope of a physical security assessment.
Unlike more limited evaluations, such as testing fire alarms or ensuring cameras are working, a physical security audit is a 360-degree review. It covers everything from your building and security systems to plans and procedures to potential threats from your surrounding environment.
Some organizations have the expertise and resources to perform physical security assessments in-house, but many companies turn to security consultants who specialize in them. When possible, it’s best to use your security team’s knowledge and engage a specialist—an extra set of eyes can provide fresh perspectives and catch details that might otherwise slip through the cracks.
How to Conduct a Risk Assessment
This video will help you facilitate an effective security risk assessment at your organization.
Why Are Physical Security Assessments Important?
You must be ready for remediation if an emergency does unfold, but mitigation is preferable. At its core, security should prevent adverse outcomes, be they injuries, loss of life, property damage, or theft. A physical security audit reduces the likelihood of these outcomes by identifying potential risks so you can implement security controls.
However, improved overall security through risk assessment isn’t merely preventative—it also provides benefits in several other ways.
Improve business resilience and risk management

Every company will face challenges, whether it’s severe weather, accidents, or acts of malice. An in-depth physical security assessment can identify vulnerabilities for all of these scenarios and curative measures for risk mitigation. By implementing these safeguards, you can improve your business resilience and give your team the resources to deal with problems as they occur.
Foster a positive safety culture
One key tenet of a positive safety culture is providing an environment where employees believe you have their security and welfare in mind. By performing physical security assessments, addressing vulnerabilities, and communicating updated procedures, you’re displaying organizational commitment to safety and security.
Mitigate cybersecurity threats
While most penetration testing and cyberattack response planning are out of scope, physical security programs are critical in maintaining cybersecurity. A physical security assessment will help you identify and mitigate vulnerabilities that could lead to unauthorized physical access to vital information systems and sensitive data.
Your assessment should evaluate the effectiveness of any surveillance systems, security cameras, access controls, and security policies to ensure they meet requirements and expectations. By revealing potential physical security weaknesses, you’ll be better able to implement improved safeguards that bolster your overall cybersecurity.
Maintain regulatory compliance
In some industries, physical threat and vulnerability assessments aren’t just a good idea but a security requirement. There are a variety of regulations covering physical security—many of them related to companies storing sensitive information—but these are four of the most common:
- International Organization for Standardization (ISO) 27001, which is a comprehensive set of guidelines for information security
- The Health Insurance Portability and Accountability Act (HIPAA), a U.S. law that governs how companies can handle health data
- Payment Card Industry Data Security Standards (PCI-DSS), a security standard for any business that processes credit card transactions
- Occupational Safety and Health Administration (OSHA) Hazard Identification and Assessment, which provides industry-specific guidelines for security and hazard inspections
Consider working with security experts
While internal teams often bring valuable insights to a security assessment, engaging a security consultant or reputable security firm can significantly elevate the quality and depth of your evaluation. Professionals with broad experience in the industry, along with the proper education and training, can offer additional perspectives on threat impact and likelihood, especially when applying a layered approach to risk mitigation.
Look for providers with strong references and reputation, relevant associations and certifications, and the ability to oversee security projects from assessment to implementation. Consultants can also provide vendor recommendations tailored to your environment and expertise, helping you make informed decisions backed by practical field knowledge.
9 Steps to a Thorough Physical Security Assessment
The details and specifics will vary based on organizational and environmental factors, but the following seven areas should be part of any physical security assessment checklist.
1. Define the scope of your assessment
The first and most crucial step in conducting a physical security assessment is defining its scope. This involves determining which assets, facilities, and locations will be included in the assessment. A well-defined scope ensures your assessment is comprehensive and focused, allowing for efficient resource allocation and effective risk management.
- Identify key assets and locations
Begin by listing all the physical assets and locations that need protection. This could include corporate offices, warehouses, production facilities, or any other critical infrastructure. Consider each location’s business-critical nature and prioritize facility security accordingly. - Determine specific risks and threats
Understand the specific risks and threats associated with each location. This could involve analyzing factors such as geographic location, the nature of operations, and historical incidents. Identifying these risks will help tailor the assessment to address the most pressing concerns. - Set clear objectives
Define your assessment’s goals. Are you looking to enhance overall security, comply with regulatory requirements, or protect specific assets? Clear objectives will guide the assessment process and provide measurable outcomes. - Engage stakeholders
Involve key stakeholders early in the process to ensure alignment and gather diverse perspectives. This could include security personnel, facility managers, and executive leadership. Their input can provide valuable insights and help refine the scope. - Document the scope
Clearly document the scope of the assessment, including the assets, locations, risks, and objectives. This documentation serves as a reference point throughout the assessment process and ensures all team members are aligned.
By defining the scope at the outset, you lay the foundation for a focused and effective physical security assessment. This step ensures that all critical areas are covered and that resources are utilized efficiently, ultimately contributing to a more secure organization.
2. Inspect your facilities and sites
The first step is to evaluate the spaces and structures you’re securing. The goal is to understand both strengths and weaknesses, remembering that physical security management isn’t just about preventing crime but also protecting against accidents, security incidents, natural disasters, and other potential threats.
Here are some of the most common items to consider during a building security assessment:
- Is there appropriate lighting in both internal and external spaces?
- What are the sightlines like around entrances and exits to the facility?
- Have electrical systems and wiring shown any signs of degradation?
- Are there any plumbing issues that could lead to building damage or accident hazards?
- Do all doors, windows, gates, and other points of entry close and lock properly?
- Are areas with critical assets physically partitioned from spaces with general access?
- Is safety equipment, like fire extinguishers and smoke detectors, all in good working order?
3. Audit your physical security systems
Next, you need to assess your security systems and how they cover your company’s physical spaces. Target-hardening techniques include:
- Access control systems, whether it’s biometric, card-based, or old-fashioned keys
- Personnel, including supervisors, staff in your security operations center (SOC), and security guards throughout your facility
- Surveillance cameras, monitors, and storage devices that contain recordings
- Alarm systems and supporting systems that notify local law enforcement in the event of a problem
Since all of these systems work hand-in-hand, your questions will usually involve interactions between systems and/or resources. For example:
- Are there any times of day when security personnel aren’t monitoring the CCTVs covering sensitive areas?
- Are there alarms that should go off if someone bypasses access control systems, and will they notify the right people?
- Does your surveillance camera network have any critical blind spots that would allow unauthorized access?
- Can your SOC seamlessly use all your security systems to prevent and respond to security issues as they arise?
4. Review your operating procedures
Even the most robust security systems are useless if your organization’s procedures don’t align with its security goals. For example, a company manufacturing toxic chemicals would establish the security goal of keeping the general public away for everyone’s safety. But if it leaves external doors unsecured and doesn’t partition off sensitive areas, its procedures wouldn’t reflect that goal.
In this phase of the process, you’ll assess the effectiveness of your policies and security plans. While this exercise focuses on physical security, the rise of converged security means you’ll also be touching on cybersecurity issues.
In this step, you’ll evaluate everything from security policies to emergency plans, such as:
- What kind of overnight/off-hours security presence do you maintain on-site?
- How should employees report suspicious activity or a potential security issue?
- Which essential personnel have elevated access to the facility in the event of an emergency, and how is that controlled?
- Do you have evacuation plans available and emergency exits marked?
- Have you trained all of your employees on using your two-way communication platform?
- Do you have emergency response plans for incidents like robberies or active shooter situations?
- Are all your employees aware of your plans and procedures and able to access them easily?
5. Identify physical security risks
Every business faces different risks based on a combination of internal and external factors. For example, a bank in the heart of New York City houses extremely valuable assets in a dense, urban environment, with a high volume of visitors every day.
Conversely, a vacuum repair shop in South Dakota will operate in a slower-paced environment, with fewer visitors and less valuable inventory. That’s not to say the vacuum repair shop necessarily faces fewer risks, but they’re very different from the bank’s.
Specific risk factors will vary based on your company, but these are some core topics all businesses should consider:
- Surroundings: What are the crime rates in your area, and what types of crime are most prevalent?
- Natural disasters: Are you in a region prone to specific disasters or severe weather like earthquakes, hurricanes, or snowstorms?
- Workforce: Does your company have high turnover and thus a repeated influx of new people in positions of responsibility?
- Visitors or customers: Are you in an industry with a constant stream of unknown entities at your facility?
- Inventory and assets: Do you store or possess high-value items at your facility, and how portable are they? Securing small but valuable items like gold coins differs greatly from large objects like expensive printing presses or machinery.
- Supply chain: Are there vulnerabilities in your physical security that may create supply chain risks and interrupt business operations?
During the threat identification phase, it’s crucial to employ a variety of techniques to ensure no potential risks are overlooked. Consider the following methods to identify threats and vulnerabilities:
- Conduct site visits: Physically inspect each facility to observe security measures and identify any potential weak points. Pay attention to areas like entrances and exits, lighting, and surveillance coverage.
- Interview employees and management: Engage with staff at all levels to gather insights into potential security concerns. Employees can often provide valuable information about areas that external assessments may overlook.
- Analyze environmental factors: Assess the surrounding environment for external threats such as high crime rates, nearby industrial activities, or susceptibility to natural disasters. Understanding these factors can help in tailoring security measures accordingly.
- Review historical incident data: Analyze past security incidents within the organization to identify patterns or recurring vulnerabilities. This data can guide future threat identification efforts and improve overall security posture.
By using these threat identification techniques, you can comprehensively understand your threat landscape and develop targeted strategies to mitigate risks effectively.
6. Anticipate insider threats
Threats to your physical security don’t always come from external sources. Potential security breaches may come from inside your organization, and you must work to prevent or mitigate insider threats proactively. Your insider threat assessment should focus on pinpointing vulnerabilities that could be exploited by insiders (employees or staff members), such as areas with inadequate surveillance, overly permissive access controls, or insufficient segregation of duties.
You can also consider implementing the principle of “least privilege,” where individuals have access only to what is necessary to perform their job functions and no more. These strategies, paired with an overall culture of security awareness among employees, can significantly reduce the risk of insider threats.
7. Assess specific threats and vulnerabilities
Once you have a handle on your company’s risks, you can assess the most realistic threats. The two most important factors to consider are the likelihood of a threat materializing and its potential impact on your business. For example, a meteor striking your office would be devastating, but the event is unlikely enough to be more or less ignored.
While assessing threats, you’ll look for potential vulnerabilities and ways to fix them with security measures. For example, a retail establishment in an urban environment would view theft as a key threat. The occasional stolen candy bar won’t put anyone out of business, but losses add up over time. With that in mind, they’d look at retail loss-prevention strategies in the context of their business to minimize theft, such as:
- Having a security guard at the entrance as a visible means of deterrence
- Constantly monitored surveillance cameras
- Keeping valuable merchandise in secured areas of the store
- Training staff on how to deal with shoplifters and whether they should engage them
- Lighting with motion sensors to deter loitering in the evening and overnight
- Rollup doors or external gates to provide an extra layer of security while the business is closed
8. Document and report on your assessment
Reporting and documentation formalize your physical security assessment and turn insights into action. Clear, well-structured reports help communicate risks, prioritize response efforts, and support leadership in making data-driven security decisions.
Clear documentation also helps convey the urgency of certain risks and the rationale behind proposed mitigation strategies to stakeholders. Tailor your reports to different audiences, such as executives, security teams, and regulatory bodies, to ensure the information is accessible and actionable.
Many organizations benefit from using ordinal lists or severity charts to visually rank threats from low to high priority, helping stakeholders easily understand where attention is most needed.
By following these best practices, your documentation will formalize the assessment process and enhance communication, compliance, and continuous improvement in your organization’s security efforts.
- Use standardized templates: Implement standardized reporting templates to ensure consistency and completeness across all assessments. Templates help capture all necessary information systematically, making it easier to compare data over time.
- Incorporate visual aids: Use severity charts, graphs, and diagrams to visually represent risks and mitigation strategies. Visual aids can help stakeholders quickly grasp the urgency and scope of identified threats.
- Combine qualitative and quantitative data: Blend qualitative insights, such as expert opinions and scenario evaluations, with quantitative data like risk quantification and financial impact analyses. This combination provides a comprehensive view of potential threats.
- Tailor reports to the audience: Customize the detail and focus of reports based on the intended audience: executives, security teams, or regulatory bodies. Ensure the content is accessible and relevant to each group’s needs.
- Maintain comprehensive records: Keep thorough records of all findings, recommendations, and actions taken. These documents are a reference for future assessments and demonstrate due diligence for compliance and insurance purposes.
- Regularly update documentation: Approach documentation as dynamic resources that require regular updates to reflect evolving threats, mitigation strategies, and organizational priorities. Consistent reviews ensure your security posture remains effective and aligned with current needs.
Effective reports often combine qualitative methods, such as expert opinion or scenario-based evaluations, with risk quantification to express the potential financial impact of a threat. For example, a breached access point might be rated as “high” in terms of severity due to the sensitive nature of the assets it protects, and the report might estimate the cost of remediation versus the cost of a potential breach. These cost/benefit analyses provide a valuable lens for evaluating the most feasible and urgent mitigation efforts.
When you maintain comprehensive records, you demonstrate due diligence in the event of audits or insurance claims. Thorough documentation aids in regulatory compliance and serves as a valuable reference for future assessments, helping you track risk evolution and the effectiveness of security strategies over time. These living documents allow your organization to adapt to changing threats and improve your security posture.
9. Review and update regularly
Just like your physical security is not static, your physical security assessment shouldn’t be a one-and-done process. Encourage your physical security staff, stakeholders, and anyone involved in the assessment process to conduct regular reviews to adapt to evolving threats, changes in the organizational environment, and advancements in security technology.
You can use tools such as after-action reviews or redo the assessment report entirely. Perform these updates consistently—perhaps biannually—to ensure your security measures remain effective and aligned with your organization’s objectives.
A Proactive Approach to Improving Physical Security
Security professionals face a constantly evolving threat landscape, and trying to predict what’s coming next and meet their organization’s security needs can feel daunting. Between weather, worldwide pandemics, bad actors, and the vagaries of life, many factors are outside your control.
However, you control your company’s preparedness to meet the unknown. By proactively identifying realistic threats and determining how your physical security shapes up against them, you can anticipate problems before they happen. You might not be able to see every hazard lurking, but you’ll have confident procedures to activate and trained individuals ready to act on known and unknown threats.