How to Build a Ransomware Resilience Plan
This October marks the 20th anniversary of Cybersecurity Awareness Month. Now more than ever, organizations need a plan to face the ever-evolving threat of ransomware attacks.
In this episode, Heather Engel, Managing Partner at Strategic Cyber Partners, shares invaluable insights on building an effective ransomware attack response plan and navigating the complex decisions before, during, and after ransomware incidents.
Listen in to learn how to:
- Protect and recover critical systems and data
- Train your team to stay vigilant against social engineering
- Consider your options before paying a ransom
- Mitigate reputational risk with effective communication
For more information on mitigating the risk of cyberattacks, check out the Cybersecurity and Infrastructure Security Agency.
The Employee Safety Podcast is hosted by Peter Steinfeld, SVP of Safety Solutions at AlertMedia.
You can find this interview and many more by following The Employee Safety Podcast on Spotify or Apple Podcasts.

More Episodes You May Be Interested In
-
 How Zendesk Aligns Systems and Security
How Zendesk Aligns Systems and SecuritySafety and security leaders need relevant, accurate metrics to properly evaluate the effectiveness of their systems and processes. Some systems are not designed to generate metrics at all, so it’s up to the organization to develop reporting systems from scratch. Scott Napier, Global Systems and Technology Lead at Zendesk is tackling this by capturing data…
-
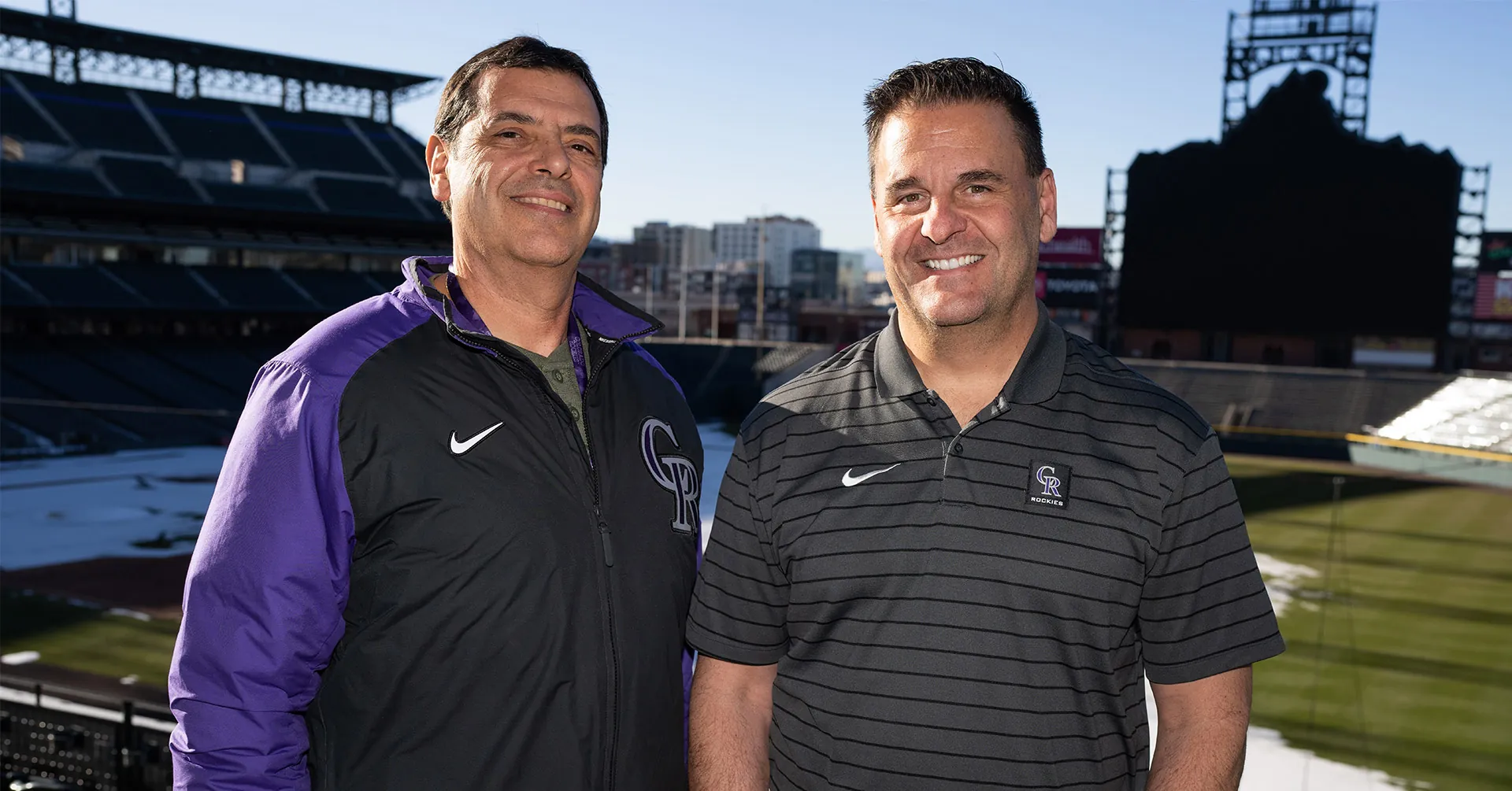
 The Colorado Rockies on the Intersection of Security and Technology
The Colorado Rockies on the Intersection of Security and TechnologyFor the Colorado Rockies, teamwork is the key to success on and off the baseball field. This episode features Tony Lopez, Senior Director of Security, and Michael Bush, Senior Director of Information Systems at the Rockies. From securing 50,000 fans to scanning the skies for drones over Coors Field, Tony and Michael work together to…
-
 How to Leverage Technology and Automation to Improve Physical Security
How to Leverage Technology and Automation to Improve Physical SecurityIn today’s threat landscape, physical security leaders face mounting risks with increasing resource constraints. At Datadog, a SaaS-based data analytics platform, Julius Jayasekaran embraces the lean security model by leveraging technology. As Global Head of Physical Security with decades of experience in security operations, Julius discusses how utilizing technology and automation empowers his modern security…