A bodyguard alone cannot solve today’s executive security risks. This guide explains how modern executive protection programs identify threats early and prepare teams to respond.

Close Protection vs. Executive Protection: A Modern Approach to Protecting Leaders
During what should have been a routine rush-hour commute in one of North America’s safest cities, a cryptocurrency CEO experienced a terrifying—but increasingly real—worst-case scenario.
In November 2024, multiple assailants forced WonderFi CEO Dean Skurka into a vehicle in downtown Toronto, attacking him in one of the city’s busiest business districts. He was held for several hours before being released unharmed after roughly $1 million CAD was paid. No suspects have ever been publicly charged.
These incidents have a name. Known as “wrench attacks,” they involve criminals using physical force or threats to compel victims to transfer cryptocurrency.
And it’s not just crypto executives at risk. As digital wealth becomes easier to move and harder to trace, criminals are increasingly targeting high-profile individuals believed to control valuable assets.
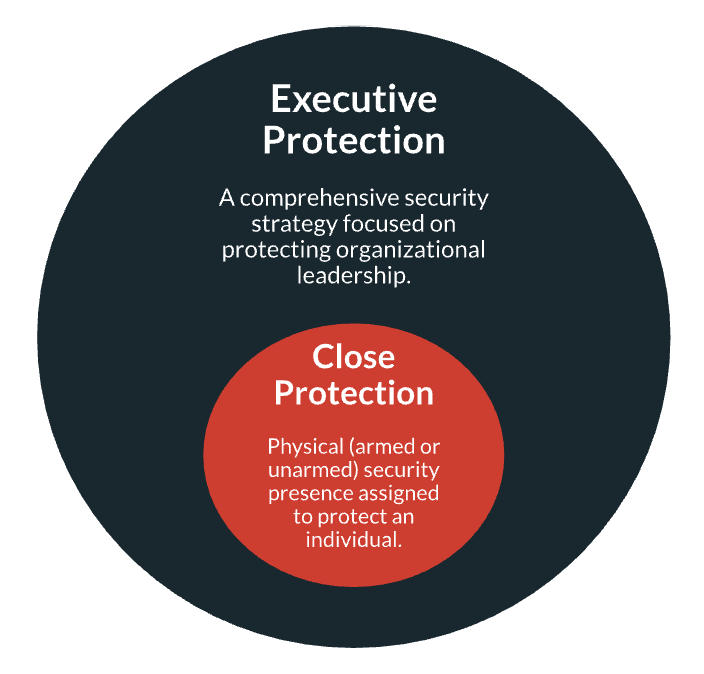
This shift has forced the security industry to rethink how leaders are protected. The discussion around close protection vs. executive protection has become central to modern risk management. Close protection professionals safeguard executives in real time, while broader executive protection strategies anticipate threats and coordinate security before an incident ever unfolds.
Here’s what you need to know.
Download Our Executive Protection Tabletop Exercise Template
Close Protection vs. Executive Protection: What’s the Difference?
Close protection is a subset of corporate executive protection, the broader security strategy organizations use to keep senior leaders safe. Close protection refers to security professionals who remain physically near the individual they are assigned to protect. Depending on the situation, this may involve bodyguard services at public appearances, dedicated security drivers during travel, or long-term close protection services assigned to a specific executive.
This visible security presence acts as both a deterrent and a rapid-response safeguard. Trained personnel monitor the immediate environment and intervene if a threat develops.
Preventing those threats in the first place falls within the broader executive protection strategy. Security teams analyze risk, evaluate travel and event exposure, and coordinate protective measures so the right safeguards and personnel are in place before an executive arrives.
The limitations of close protection
Close protection refers to private security personnel assigned to remain physically near an individual to deter or respond to potential threats. Their role focuses on immediate physical safety and rapid emergency response if a security incident occurs.
The level of close protection deployed typically depends on risk and budget. Basic security guards may cost around $30 per hour, while trained security drivers and executive protection agents can cost several hundred dollars per day, especially if armed or traveling with the executive. These costs can increase significantly when multiple agents, travel logistics, or long-term coverage are required.
The cost is not the only limit to close protection services. It is primarily designed to address threats of violence and cannot mitigate many other risks executives may face, including:
- Severe weather—storms, flooding, or extreme heat that disrupt travel or safety
- Transportation disruptions—airport closures, road shutdowns, or transit failures
- Communication outages—loss of cellular or internet connectivity during travel
- Legal or regulatory changes—local laws or restrictions that affect personnel
- Public health risks—disease outbreaks or medical emergencies
- Environmental hazards—poor air quality or other environmental conditions
Because of these limitations, close protection works best as one component within a broader executive protection strategy that anticipates and plans for a wider range of risks.
Executive protection beyond the bodyguard
Executive protection expands security beyond the immediate presence of guards. The focus shifts to identifying risks before they reach the individual being protected. Instead of reacting as situations unfold, security teams examine where leaders travel, whom they interact with, and which environments may expose high-net-worth individuals and other senior leaders.
Teams also monitor emerging issues that could affect personnel. Security teams evaluate risks—from crime trends to infrastructure disruptions—and develop plans to reduce exposure before an executive arrives on site. These programs often operate alongside broader security services, including personal protection or bodyguard services during public appearances.
Executive protection also requires coordination across multiple functions. Security teams work with travel planners and organizational leadership to align planning and response. Close protection personnel may still play an important role, especially when leaders need a low-profile protective presence during travel or public engagements. Their work fits into a larger framework designed to identify vulnerabilities, plan contingencies, and support leaders wherever their responsibilities take them.
Executive Protection | Close Protection | |
| Scope | Organization-wide strategy to protect executives across travel, events, and daily operations, particularly for high-net-worth individuals and visible leadership roles. | Physical, proximity-based protection provided by security personnel, often delivered through personal protection or bodyguard services. |
| Time horizon | Long-term and preventative. | Immediate and reactive, focused on deterrence and emergency response if a threat develops. |
| Risk inputs | Threat intelligence, travel risk assessments, business impact analysis, and event security planning. | Physical security awareness and immediate environmental observation. |
| Operational model | Proactive planning and risk mitigation across multiple environments. | Protective presence that deters threats and responds to incidents. |
| Stakeholders involved | Security leadership, travel teams, corporate leadership, and external partners delivering security services. | Security agents, drivers, or guards assigned to the individual. |
| Level of planning and coordination | High—requires advance planning and cross-team coordination. | Moderate—focused on executing protective duties in real time. |
| Role of intelligence and monitoring | Central—used to identify threats and inform planning. | Limited—relies primarily on real-time observation. |
| Typical scenarios | Executive travel planning, event security preparation, and risk monitoring. | Executive escorts, secure transport, and on-site protection. |
Why Close Protection Alone Is Not Enough for Modern Executive Risk
Close protection still plays an important role in executive safety, but today’s threat picture extends far beyond what a guard or agent can manage through physical proximity alone. Risk can emerge well before an executive arrives at a venue or steps out of a vehicle.
Exposure may develop through public appearances, travel, social media activity, doxxing, impersonation, reputational escalation, or sudden itinerary changes that create new vulnerabilities in real time. These realities have pushed organizations and security companies to rethink traditional security protocols and how they deploy protection operatives.
Steve Hernandez, CEO of The North Group, spoke about this shift in an interview on The Employee Safety Podcast. In his view, executive risk management has moved beyond reacting to threats in the moment and toward identifying them earlier.
He illustrated that point with a story about protecting a well-known political commentator at a stadium speaking event in Michigan. Before the event began, Hernandez conducted an advance visit to the venue to assess the environment, evaluate lines of sight, and understand how someone might approach the speaker. He brought tools such as binoculars and a rangefinder to help evaluate distances and vantage points, but the venue’s operations manager reportedly questioned why that level of preparation was necessary.
That reaction reflects a common misunderstanding about how modern executive protection works. To someone focused only on the event itself, the venue may have seemed secure enough. But Hernandez’s advance work was not limited to deciding where a guard should stand once the executive arrived. Instead, it focused on understanding how an adversary might exploit the environment before or during the appearance—an approach that protection operatives and experienced CPO teams increasingly emphasize in their planning.
What he found was that the most immediate vulnerability was not some dramatic long-range threat. It was the public access point closest to the executive—the rope line, where attendees could gather, move close, and potentially create an opening for confrontation or harm. The real risk came from the event layout, crowd access, and the ease with which someone could get close to the principal in a space that otherwise appeared controlled.
That example shows why close protection alone is no longer enough. A physical security presence matters once the executive is in motion or on site. But it does not, by itself, account for the broader conditions that create risk in the first place.
Public events, travel, digital exposure, and fast-changing circumstances can all shape an executive’s vulnerability before a close protection professional ever has to react. As a result, many organizations now expect their security partners to combine experienced personnel, structured security protocols, and formal training or industry certifications when building protection programs.
To hear Hernandez’s full perspective on how executive protection is evolving and why protective intelligence is becoming central to modern programs, listen to the full episode.
What Does Modern Executive Protection Require?
Modern executive protection centers on foresight. Security teams need clear visibility into emerging risks, strong coordination among stakeholders, and response processes that enable them to address threats early.
The key elements of a modern executive protection program include:
- Executive risk assessment: Identify where leaders face risk.
- Protection and intelligence: Combine security presence with threat intelligence.
- Incident response planning: Prepare teams to act quickly.
- Travel and events: Assess risk during travel and public appearances.
- Security coordination teams: Align security with leadership and operations.
- Escalation response paths: Define how threats are reported and handled.
- Executive trust building: Gain executive cooperation through trust.
1. Understand the full range of executive risk
The kidnapping of WonderFi CEO Dean Skurka illustrates how executive risk can emerge in seemingly routine settings. A rush-hour commute in downtown Toronto would not traditionally be considered a high-risk environment. Yet attackers identified an opportunity, targeted the executive, and forced a ransom payment through physical coercion. In this case, cryptocurrency created a new incentive for criminals.
But crypto-related wrench attacks are only one example of how executive risk is changing. Today, security teams must assess risks across multiple areas, including:
- Public visibility: Conferences, speaking engagements, and media appearances increase an executive’s exposure and may require personal protection or coordination with security services.
- Travel patterns: Predictable routes and frequently visited destinations can make executive movements easier to anticipate and influence executive protection planning.
- Digital footprint: Social media activity and publicly shared information can reveal details that shape threat intelligence assessments.
- Online hostility: Harassment, threats, or escalating grievances directed at executives can signal elevated risk and require monitoring.
- Doxxing and personal data exposure: Publishing home addresses, family details, or contact information can significantly increase the risk for high-net-worth individuals.
- Impersonation and fraud: Attackers may impersonate executives to manipulate employees, partners, and other stakeholders.
- Reputational escalation: Corporate decisions that generate intense public backlash can increase the likelihood of targeted harassment or cyberattacks.
- Event conditions: Crowd dynamics and venue layouts influence how protection operatives manage risk during public appearances.
- Real-time operational changes: Sudden travel or schedule adjustments can introduce new vulnerabilities that require immediate coordination and response.
For this reason, modern executive protection begins with understanding the full range of potential risks. Security teams must evaluate how visibility, digital presence, travel patterns, and public engagement may intersect to create exposure. This must all be done well before an executive ever arrives on site.
2. Combine physical protection with protective intelligence
Close protection ensures the executive’s immediate safety upon arrival on site. Protective intelligence helps the security team understand the risks surrounding that appearance before the executive ever enters the environment. When these two functions work together, security teams can adjust plans early rather than react in real time.
Protective intelligence today also includes monitoring digital risks that may influence real-world exposure. Disinformation security plays an important role here. False narratives, manipulated content, and coordinated campaigns can quickly amplify hostility toward an executive or draw unwanted attention to an upcoming appearance. By monitoring disinformation activity and other online signals, security teams can identify situations that may escalate.
Consider a CEO scheduled to speak at a large industry conference. Physical protection will escort the executive through the venue and respond to any immediate issues, but protective intelligence informs the plan long before the event begins.
- Event risk review: Security teams analyze the conference location and the expected attendance. They also review the venue layout and the level of public visibility tied to the CEO’s appearance.
- Threat and online monitoring: Teams review social media activity and public commentary. They also examine recent corporate decisions that may have generated hostility toward the executive or the company.
- Travel and physical security assessment: Arrival routes, transportation plans, and hotel arrangements are reviewed to identify predictable patterns or areas where exposure could occur.
- Security plan adjustments: Teams update the security plan based on the information gathered. They may modify arrival times or change access points. They may also coordinate with venue security. In some cases, they limit proximity during meet-and-greet sessions.
- On-site protection: When the CEO arrives, close protection personnel implement the plan and escort the executive throughout the venue. They manage crowd interactions while remaining prepared to respond if a situation develops.
In this model, protective intelligence provides the context that allows physical protection to operate effectively. Security personnel are executing a plan informed by early visibility into potential risks.
3. Plan for incidents before they happen
Executive protection cannot wait until a threat appears. Security teams need to anticipate potential incidents long before an executive is exposed.
During his interview on The Employee Safety Podcast, Steve Hernandez described how his team sometimes conducts red-team exercises to prepare for this scenario. In these exercises, the team deliberately thinks and operates like an adversary. They examine the broader environment around the organization to understand how someone might realistically attempt to reach the target.
One scenario considers whether someone could approach through a contractor who regularly enters the office. Another examines whether a vendor relationship could provide proximity. The team also evaluates whether publicly available information about schedules, travel plans, or events could help predict where an executive will be. Testing these scenarios internally helps identify vulnerabilities that might otherwise go unnoticed.
The goal is to understand how an attack could unfold. Once those possibilities are identified, security teams adjust protocols, tighten access points, and coordinate response procedures before a real adversary attempts the same path.
Organizations often reinforce this type of planning through executive protection tabletop exercises. In these sessions, security teams and leadership walk through realistic scenarios—such as a threat during a public event, a disruption during executive travel, or a rapidly escalating online threat—to test how the organization would respond. Practicing these responses ahead of time prepares teams to execute the plan when a real incident occurs.
4. Manage risk during travel, events, and public exposure
Executives face their greatest exposure outside controlled environments. Travel, public appearances, conferences, and media events place leaders in settings where security conditions can change quickly. These environments also bring large numbers of people into the same space.
Managing these situations requires careful planning and coordination. A VIP protection professional may accompany the executive, but security teams also need to understand the environment, identify potential vulnerabilities, and adjust plans as conditions evolve.
As discussed earlier, Steve Hernandez described reviewing a stadium venue ahead of a speaking engagement. During the advance visit, he used tools to evaluate distances and sight lines. He also assessed how someone might approach the stage. The assessment later revealed that the most realistic vulnerability was the rope line where attendees gathered near the speaker.
Examples like this show how travel and public events introduce risks that are not always obvious at first glance. Crowd movement affects proximity to the executive. Access points and venue layouts influence how people move through the space. Last-minute schedule changes can also alter exposure.
For this reason, executive protection teams evaluate event environments before an appearance. They coordinate with venue security and local law enforcement when needed. Teams also monitor conditions throughout the event and adjust the plan if circumstances change. This preparation helps reduce exposure while allowing leaders to carry out their responsibilities safely.
5. Coordinate security across teams and functions
Executive protection does not operate in isolation. Protecting a senior leader requires coordination across multiple teams that influence travel risk management, communications, operations, and safety. Without that coordination, critical information can be missed and response efforts may become fragmented.
Security teams must work closely with internal and external partners to maintain visibility into evolving conditions and ensure the right safeguards are in place.
Key groups that typically need to coordinate include:
- Corporate security teams: These teams oversee vulnerability and risk assessments across the organization. They also develop protection plans and maintain incident response protocols.
- Executive assistants and scheduling teams: Their work includes managing executive travel plans and event logistics. They also track real-time itinerary changes that could affect security.
- Travel and logistics teams: Flights, hotels, and transportation fall under their coordination. Local arrangements that support executive movement are also part of their responsibilities.
- Communications and PR teams: Media coverage and public attention are monitored by communications staff. They also assess reputational escalation that could increase security concerns.
- Legal and compliance teams: Regulatory considerations often require legal guidance. These teams also review potential legal risks associated with events or locations.
- Human resources and internal operations: Employee communications during security situations may involve human resources. Workplace considerations tied to executive protection activities also fall within their scope.
- Insurance and risk management teams: Kidnap and ransom (K&R) coverage is coordinated through risk management. These teams ensure crisis response procedures align with insurer requirements.
- Cybersecurity and digital risk teams: Online threats and impersonation attempts are monitored by cybersecurity specialists. They also analyze digital signals that may affect executive safety.
- Local security partners: Venue security and contracted protection services provide on-the-ground support. Law enforcement coordination may also occur when additional security resources are needed.
Each of these groups contributes information that can influence executive risk. Travel changes, media announcements, operational disruptions, or online escalation can all affect exposure and require security teams to adapt quickly.
When coordination works well, security teams gain early visibility into emerging risks and can adjust protection plans accordingly. The next step is ensuring that when a threat or incident does occur, everyone knows exactly how it should be reported and handled through clearly defined escalation paths
6. Establish clear escalation and response paths
Even the most thorough protection plan cannot eliminate every risk. When a threat emerges, organizations must ensure that the right people are notified quickly and that decisions can be made without confusion or delay. Clear escalation paths define who receives information, who evaluates the situation, and who has the authority to act.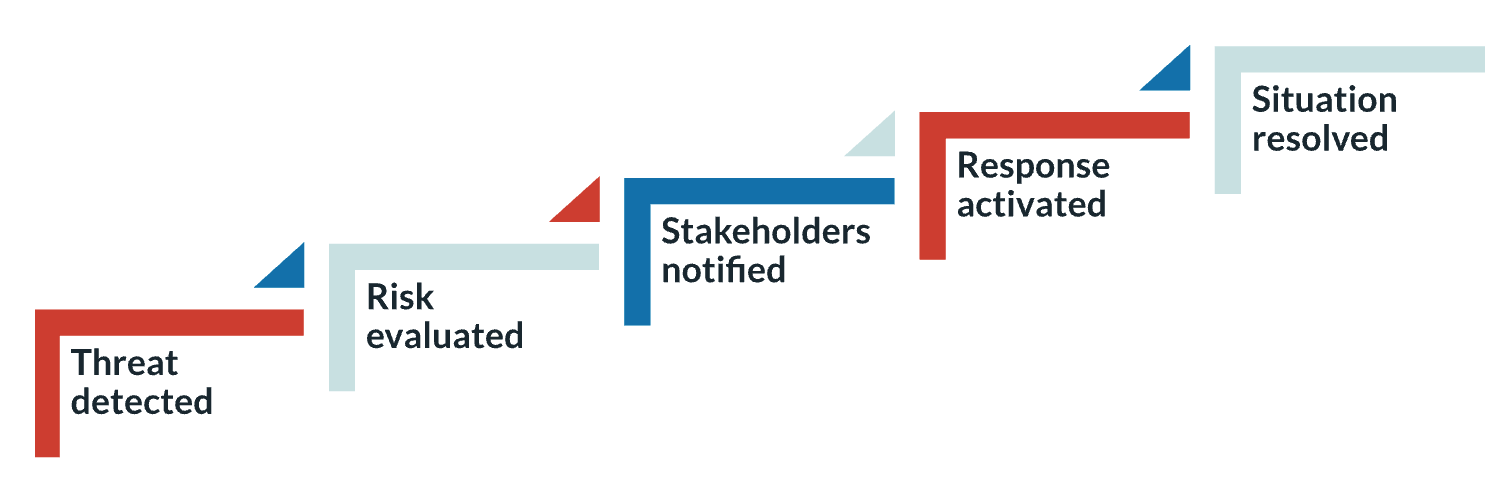
Without a defined process, teams may hesitate, duplicate efforts, or fail to share critical information in time. Establishing response workflows ensures that when security teams detect a credible concern, whether it is an online threat, a developing situation at an event, or suspicious activity near an executive, everyone understands the next step.
7. Build trust and cooperation with executives
The final step in an executive protection program is building a security culture that allows leaders to trust the security team’s guidance during high-pressure situations. When an incident occurs, executives must be able to rely on the professionals around them and feel confident that their safety is the priority. That trust is built well before a crisis through consistent communication and clear expectations.
Security teams should make an effort to explain risks in practical terms and provide guidance that helps executives understand why certain precautions are necessary. When leaders are informed and involved, they are far more likely to follow security recommendations during travel, events, or unexpected incidents.
To build that trust, security teams should:
- Be transparent about risks so executives understand the reasoning behind security measures
- Provide clear guidance on travel, public appearances, and digital exposure
- Communicate early and often when plans change or new risks emerge
- Respect the executive’s responsibilities and schedule while maintaining safety protocols
When executives trust the people responsible for their protection, they are more likely to cooperate with security measures and respond quickly to guidance in developing situations. That cooperation can make the difference between a controlled response and a chaotic one when an incident unfolds.
When Is Close Protection Still the Right Tactic?
Sometimes there is no substitute for boots on the ground. A trained security professional physically present with an executive provides immediate protection that planning, monitoring, and intelligence alone cannot match. Close protection remains a vital part of keeping leaders safe. It simply works best when used as part of a broader executive protection strategy.
Organizations often deploy close protection during situations that naturally increase exposure. High-profile public appearances, major conferences, and large public events can place executives in crowded environments where proximity to the public is unavoidable. Similarly, executive travel—especially to unfamiliar or elevated-risk locations—can introduce unpredictable conditions that benefit from having trained security personnel nearby.
Close protection may also be appropriate during periods of heightened threat activity, such as when a leader receives credible threats or public controversy increases attention on a company or its leadership. In some cases, risks may also originate closer to the organization itself.
Through processes such as insider threat assessments, organizations may identify employees, contractors, or other individuals with legitimate access who could pose a concern. Situations like these can make managing physical proximity especially important. In these moments, having security professionals present allows organizations to control access, respond quickly to developing situations, and maintain oversight of the executive’s immediate environment.
How to Strengthen Your Executive Protection Plan
Executive protection plans should not remain static. As organizations grow, leaders take on new public roles, and threat environments change, protection strategies must be reviewed and refined. Regular evaluation helps ensure that security teams remain focused on the most relevant risks and that response procedures remain clear when situations develop.
Organizations can strengthen their executive protection plans by focusing on a few key areas:
- Review risk levels regularly to ensure protection strategies reflect current threats, travel patterns, and executive visibility.
- Identify vulnerabilities and likely threat scenarios by evaluating how executives interact with public environments, digital platforms, and external partners.
- Clarify monitoring and escalation responsibilities so teams understand who watches for emerging risks and how concerns should be reported.
- Test security plans and response workflows through exercises such as tabletop scenarios that allow teams to walk through potential incidents and identify gaps before a real event occurs.
Taken together, these steps help organizations move beyond a reactive approach to protecting leadership. Close protection remains the most visible part of executive security, but it represents only one element of a broader strategy.
Modern executive protection programs combine physical security controls with risk assessment, protective intelligence, operational coordination, and clear response planning. Programs that anticipate threats and coordinate teams allow organizations to protect their leaders while leaders continue their work with confidence.
Preparation does not stop with written plans. Security teams need opportunities to walk through realistic scenarios and test how decisions will be made. These exercises help identify gaps before a real incident occurs.
Download the Executive Protection Tabletop Exercise Template to begin testing and strengthening your response planning.





